About me
Hello! 👋🏾
I believe security is more than just following rules, it’s about building resilience. In my experience supporting GRC efforts and IT initiatives, I’ve seen that the most effective strategies are proactive, not reactive. I’ve worked with organizations to move beyond box-checking by helping implement practical security and compliance frameworks that meet regulatory requirements and support long-term business growth.
I specialize in designing practical, adaptable security programs that align with business goals. From identifying vulnerabilities, assessing risks or implementing controls, I focus on maintaining the integrity, confidentiality, and availability of data. This includes deploying strong measures like encryption, access controls, and secure cloud configurations to meet regulatory requirements.
What drives me is a genuine curiosity about how systems, people, and policies connect; from cloud environments to evolving regulatory requirements. I enjoy working with cross-functional teams, streamlining processes, and strengthening organizational resilience.
My approach balances risk assessments, automation where possible, and continuous monitoring to keep data secure and business moving forward. I'm also expanding my expertise in cloud security and Infrastructure as Code, building hands-on skills in Terraform to define security controls as code, automate provisioning, and adapt quickly to emerging challenges.
Let’s connect to discuss how I can help your organization scale securely.
GRC Projects
Student Well-being App – Security & Compliance Implementation
Led the development of a student well-being app, that integrated AI-driven insights while ensuring data security, privacy, and compliance with UAE data protection laws. Applied NIST 800-30 for risk assessment, FIPS 199 for security categorization, and ISO 27001-aligned controls, reducing residual risk by 35%.

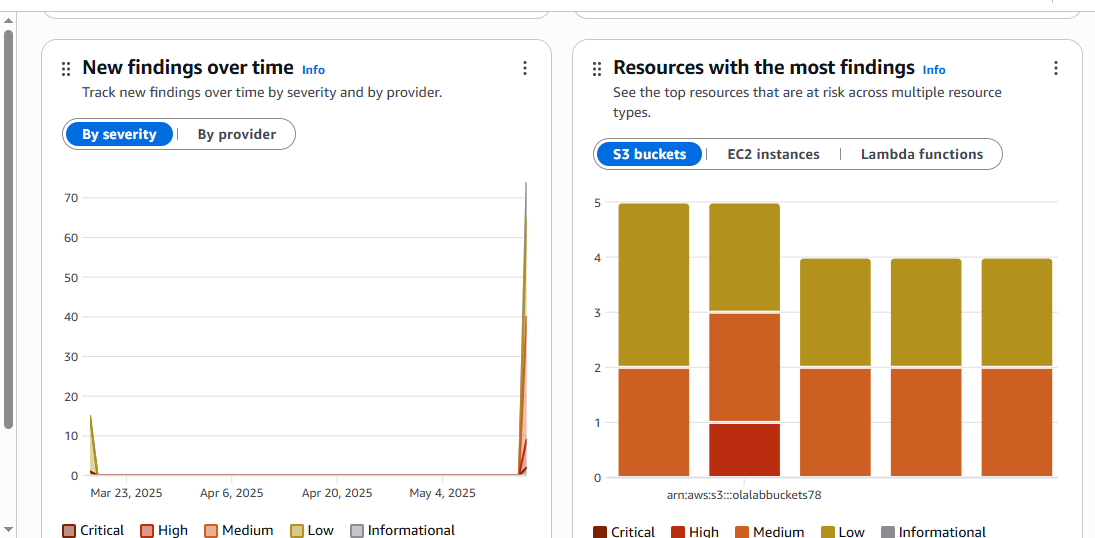
Automated S3 Remediation with AWS Config & Systems Manager-Utilized AWS Config and AWS Systems Manager Automation to enforce block access on public Amazon S3 buckets. The system continuously monitors for any disabled Public Access Block settings, automatically triggers a remediation runbook to restore privacy, and maintains detailed audit trails. With this, organizations can prevent data leakage, ensure continuous policy compliance with security best practices.
Secure AWS Account Governance- Implemented a robust AWS account governance framework that enforces least-privilege identity controls (IAM policies & MFA), centralizes audit logging, and automates compliance checks via AWS Config rules deployed with CloudFormation.
AI Vendor Risk Assessment- A vendor risk assessment for integrating a third‑party AI analytics solution, detailing the risk methodology: risk scoring, mitigation strategies, and recommendations.
Internal Cybersecurity Audit- This project simulates a real-world internal audit designed to evaluate the current security posture, identify vulnerabilities, control categorizations, and compliance checklists aligned with ISO 27001:2022, PCI DSS, SOC 2, and UAE Central Bank regulations.
Cloud Security Assessment – Conducted a security assessment of AWS environments, focusing on IAM configurations, Secrets Manager policies, and S3 access controls. By identifying users, roles, permissions, and misconfigurations, organizations can strengthen their security posture and mitigate risks associated with cloud-based threats.
Enforcing Least Privilege with CheckNoNewAccess- Implemented CheckNoNewAccess to enforce the principle of least privilege in AWS environments. By leveraging AWS Access Analyzer, this tool ensures that IAM policy updates do not inadvertently grant excessive permissions, preventing privilege escalation, and ensuring access controls align with security best practices. Some organizations integrate this API tool into their CI/CD pipeline for pre-deployment security checks.
Security Policy for a Nonprofit Organization - Developed a tailored security policy for a nonprofit organization by adapting the SANS Acceptable Use Policy template. The policy was customized to meet the non-profit sector’s unique needs, with a focus on secure donation processing, responsible use of communication platforms, and protection of sensitive community and legal aid information.
Third-Party Risk Management- Developed a risk management approach for assessing external vendors, focusing on ensuring a cloud storage provider met organization's security and compliance standards.
Secure EC2-S3 Access Control- Addressed and mitigated the risks associated with overly permissive access to sensitive customer data stored in S3 and processed by EC2 instances. Improved access controls by limiting permissions and strengthening security protocols to ensure data protection and reduce potential vulnerabilities.
ISO 27001 LEAD AUDITOR
